
Gone are the days of smashed windows and breaking into cars with crowbars. Now, a new and smarter threat has emerged that lets criminals take vehicles at the touch of a button. Connected cars can offer a gateway for cyber criminals to hack into systems.
According to figures from London’s Metropolitan Police Service (MPS), half of all car thefts in London last year were committed without using force. Instead, criminals relied on high-tech gadgets, originally designed for locksmiths, to gain access and drive away without even raising suspicion. Nearly half of the 89,000 vehicles broken into in London last year were hacked using cell-phone-sized electronic gadgets.
Automotive Industries asked Hans Roth, Director of Technology Marketing at HARMAN, how infotainment systems can help automakers to combat this threat.
Roth: It seems the hackers are targeting higherend cars, which often have more than 50 low-powered computers installed on board. One of the most common devices even tricks a car into believing that the owner’s electronic key is present by using radio transmitters that intercept key signals.
AI: Security researchers recently demonstrated that car hacking is possible using wired systems or short-range wireless such as Bluetooth. However experts confirm that similar attacks can be conducted remotely from any place on Earth. So, how does this work and what needs to be done to prevent these attacks?
Roth: As the head of the National Highway Traffic Safety Administration in the US, David Strickland, points out, “Interconnected electronics systems are creating opportunities to improve vehicle safety and reliability, but are also creating new and different safety and cyber security risks.” In other words, today’s infotainment systems provide full Internet connectivity with all the benefits of real-time updates and information. However, such access can also be an open door to malicious software.
AI: Can a virus disrupt the operation of the infotainment system?
Roth: It can cause errors in music playback, navigation and potentially corrupt the multimedia display. Equally intrusive, malware can lurk unnoticed on a system and siphon any personal and private information that may be on the infotainment hub or contained on linked devices back to another source. An even bigger concern is the potential for malware to migrate via the infotainment system to other in-car networks such as the controllerarea- network bus (CAN bus). This links infotainment to the vehicle’s critical systems. Attackers could – at least in theory – seize control of the engine and brakes.
AI: So how are industry leaders like HARMAN responding to the threat?
Roth: HARMAN has protected its next generation scalable infotainment platform by employing a multi-level security system that combats any possible cyber-attacks. In fact, HARMAN is the first vendor to employ a number of security standards and applications from the worlds of IT and mobile communications in the automotive industry as part of its comprehensive security approach. The main objective is to ensure that security is never limited to only certain points of attack. Because attackers always look for weaknesses security must be ensured at all levels, from the hardware to the App store.
AI: What are the consequences for the design of the system’s infrastructure?
Roth: The key is to provide an infrastructure that prevents sensitive data from being released to the outside world. All of the functions, data and files critical to the security and integrity of the system are protected inside a so-called “Trusted Execution Environment Partition.” Applications for infotainment systems, such as navigation, media players, or downloaded Apps run inside a completely different separated area called the “Rich Partition.” This Application Domain, running automotive grade Linux with HTML5 as the application environment, for example, offers a first line of defence with the proven security techniques used by mobile devices, such as data encryption and network security.
AI: Does this offer a sufficient level of security?
Roth: No, but the security technologies I just mentioned already offer a strong line of defence against cyber-attacks because this means they are isolated from all system-relevant, critical processes and can therefore do no harm. Messages between the domains are strictly controlled by, for example, a white list for CAN messages that only allows pre-defined messages to pass the firewall. Both domains can run the same or different operating system, such as QNX or Linux. The split-level architecture ensures that the vehicle domain remains separate. In the event that malicious code penetrates the application domain, it is firewalled from affecting the critical vehicle functions – these remain free from threat.
AI: Can you share a few hardware-related details on HARMAN’s next generation infotainment platform?
Roth: Our next generation scalable infotainment platform will feature System on Chip processor systems with two, four or even more cores that will open up more security possibilities. A core can then be used strictly for security purposes and be completely separated from the other cores. Other security technologies will include a special “Trusted Zone” inside the chip set for keys and other sensitive data as well as standard security processes such as certificates, encryption and boot monitoring to detect system changes. The Apps operated inside the system will only receive the information intended for them, and their communication with the outside world will be monitored closely. On the other hand, upgrades and over-theair updates of all functions will still be possible; therefore the applications will always be up to date.
AI: How important will upgrade capabilities and Apps be to you with your next generation product line?
Roth: Extremely important. The next generation scalable infotainment platform will be based on HARMAN’s computing modules which will allow the dealer to perform hardware upgrades. Due to the open architecture of the platform additional applications and software upgrades will be possible “Over the Air,” which means while the car is driving and the infotainment system is running in normal mode. The Apps that are “on-board” will have been already approved by HARMAN and are therefore safe. As I see it, Apps that are downloaded pose the main threat. Apps that run on a server or are streamed via the cloud, on the other hand, are relatively safe. In order to leverage the eco-system of developers and simplify the development of new Apps, HARMAN will provide standardized interfaces for third party vendors. Here, too, security will be maintained because Apps will be tested and approved. Once deployed and downloaded, these codes will never be able to gain unauthorized access to the trusted partition.
AI: How does HARMAN plan to support smartphones?
Roth: Smartphones will remain a key feature of the next generation scalable infotainment platform. However, they will not pose a risk due to the dedicated protocols – again with predefined access to vehicle information. HARMAN’s strategy revolves around controlling all of the integration technologies, functions and operating systems required to engage in mobile communications.
AI: How would you summarize HARMAN’s future security strategy in a nutshell?
Roth: By combining virtually all state-of-the-art techniques our industry-first split-domain architecture will offer a strong firewall between the domains and make the system extremely robust and resistant to hacking threats. Thereby, HARMAN’s new infotainment platform architecture points the way forward in meeting the highest security requirements, so that the fully connected vehicles of the future will remain safe from cyber-attacks.









More Stories
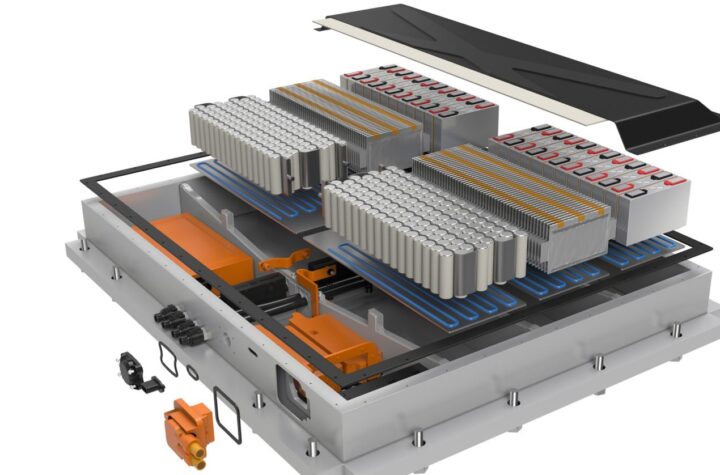
DuPont materials science advances next generation of EV batteries at The Battery Show
How a Truck Driver Can Avoid Mistakes That Lead to Truck Accidents
Car Crash Types Explained: From Rear-End to Head-On Collisions